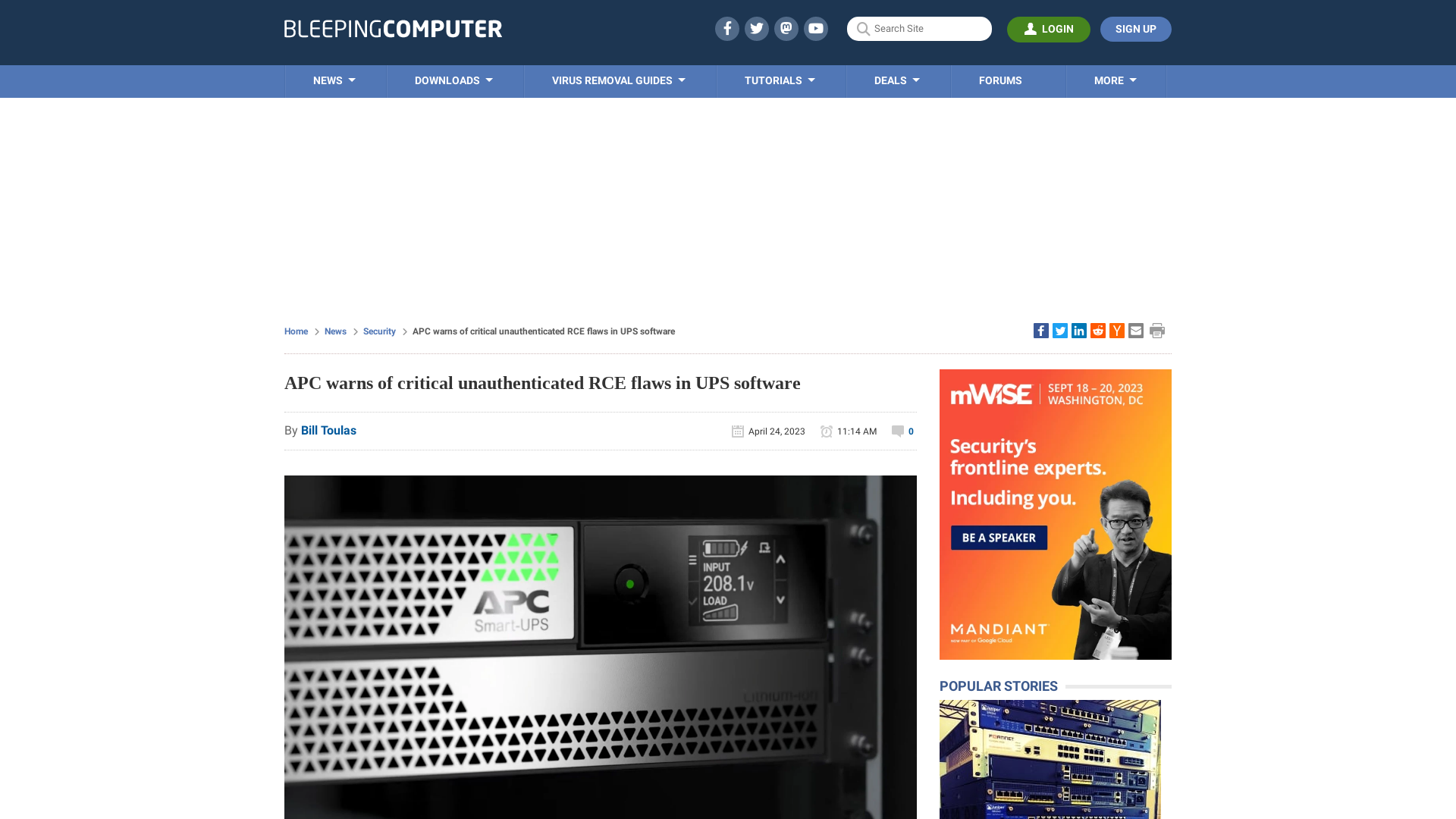
Qakbot/Qakbot_BB25_24.04.2023.txt at main · pr0xylife/Qakbot · GitHub
https://github.com/pr0xylife/Qakbot/blob/main/Qakbot_BB25_24.04.2023.txt
Hacker Group Names Are Now Absurdly Out of Control | WIRED
https://www.wired.com/story/hacker-naming-schemes-spandex-tempest/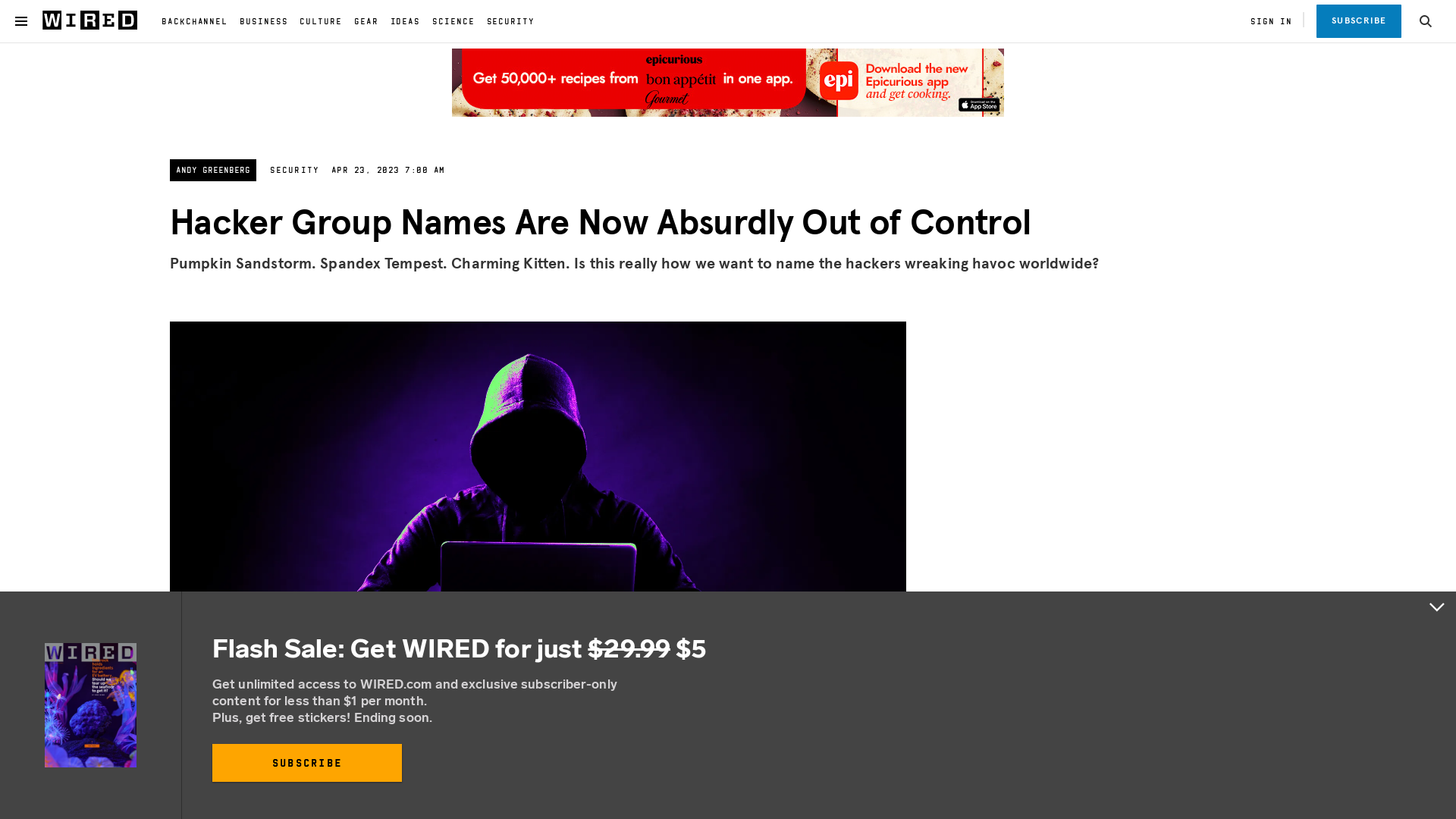
Analysis of VirtualBox CVE-2023-21987 and CVE-2023-21991
https://qriousec.github.io/post/vbox-pwn2own-2023/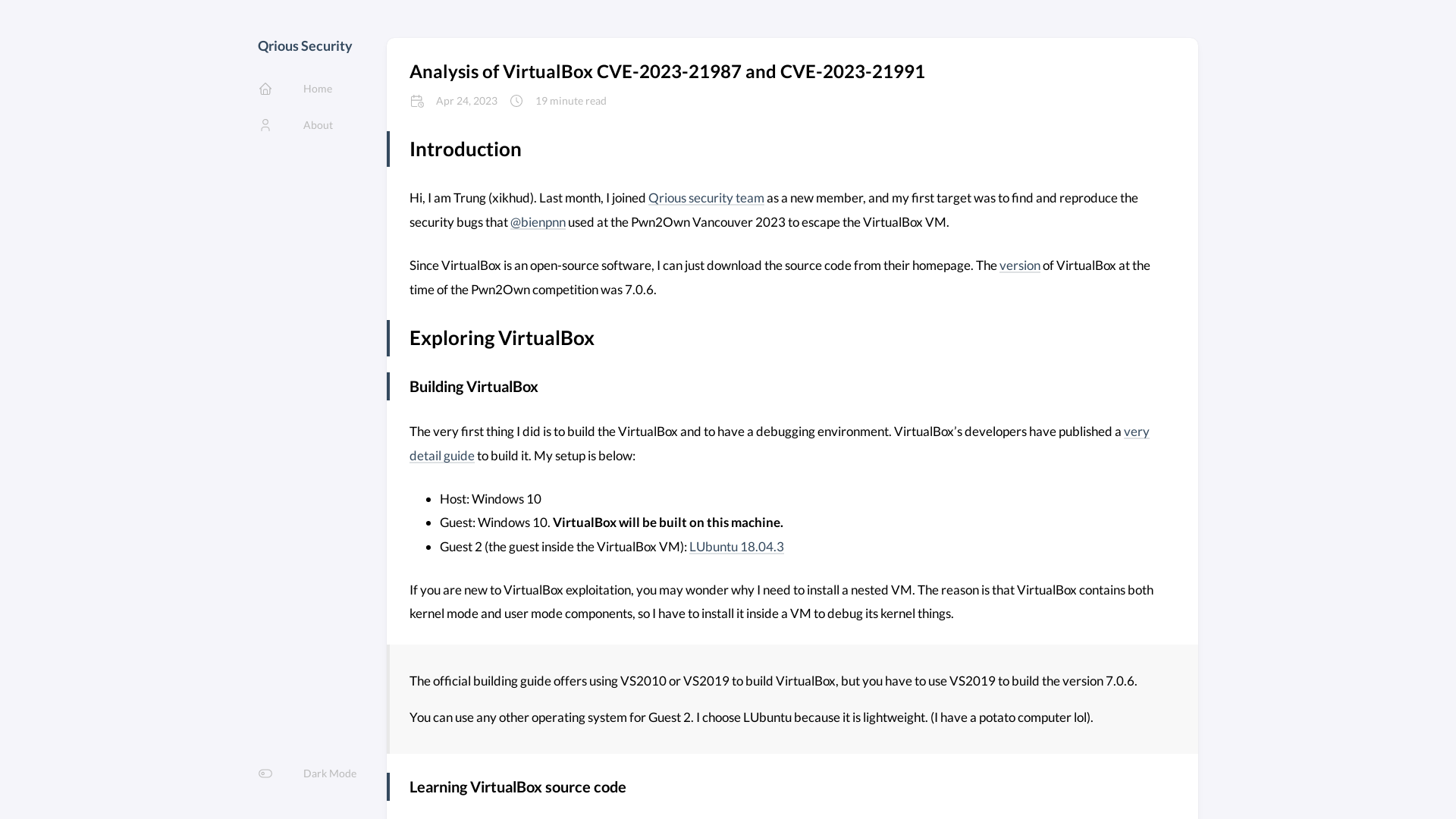
HITBAMS – Your Not so “Home” Office – Soho Hacking at Pwn2Own | NCC Group Research Blog | Making the world safer and more secure
https://research.nccgroup.com/2023/04/24/hitbams-your-not-so-home-office-soho-hacking-at-pwn2own/
Introducing VirusTotal Code Insight: Empowering threat analysis with generative AI ~ VirusTotal Blog
https://blog.virustotal.com/2023/04/introducing-virustotal-code-insight.html
Hackers can breach networks using data on resold corporate routers
https://www.bleepingcomputer.com/news/security/hackers-can-breach-networks-using-data-on-resold-corporate-routers/
Attacking O365 with TeamFiltration Part 2 - Enumeration - YouTube
https://youtu.be/YyuxEuzQa9k
Tomiris called, they want their Turla malware back | Securelist
https://securelist.com/tomiris-called-they-want-their-turla-malware-back/109552/
Detecting and decrypting Sliver C2 – a threat hunter's guide - Immersive Labs
https://www.immersivelabs.com/blog/detecting-and-decrypting-sliver-c2-a-threat-hunters-guide/
CodeQL query to detect RCE via ZipSlip - $5,500 bounty from GitHub Security Lab - YouTube
https://youtu.be/F95U912u7OQ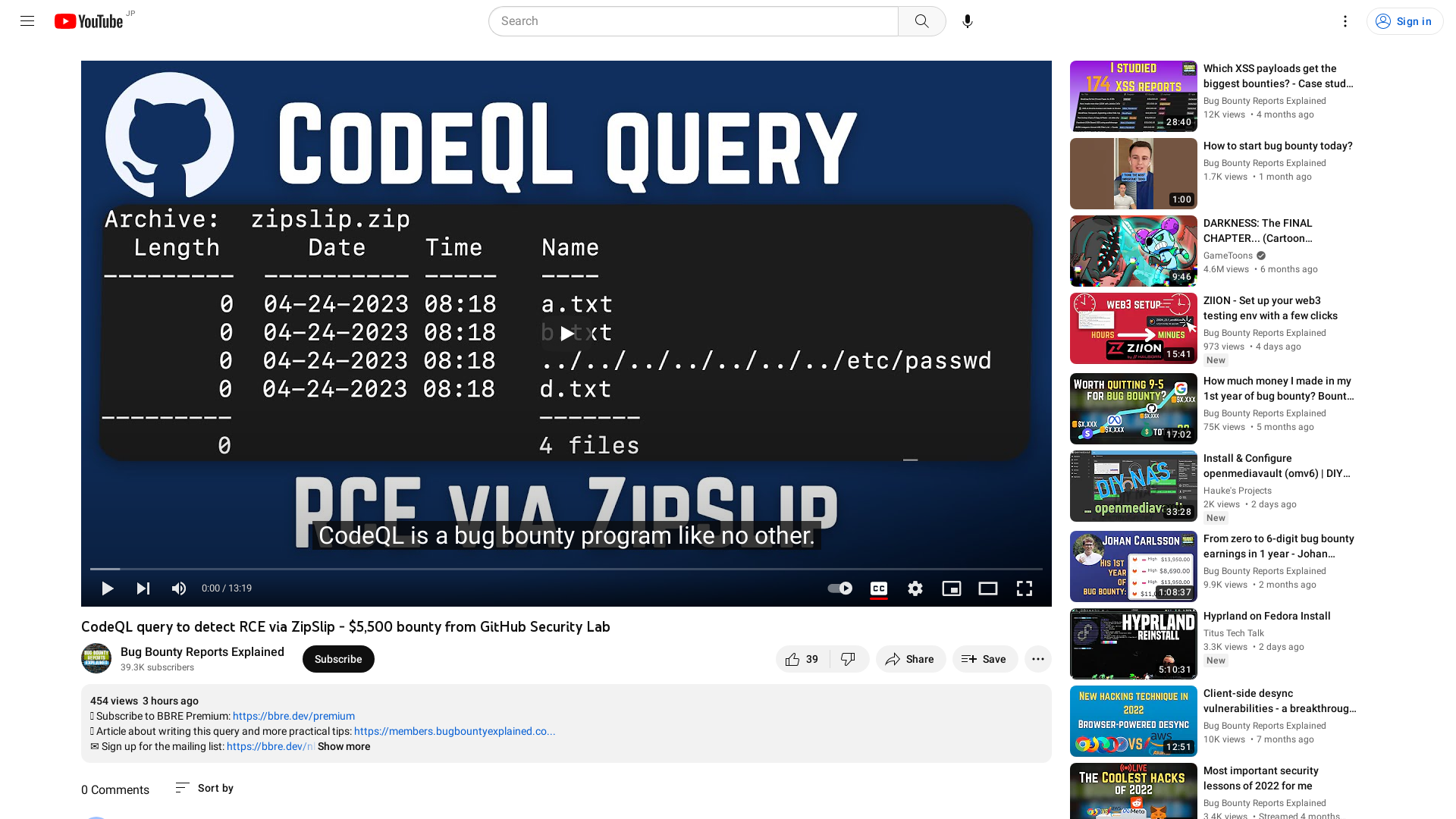
Andy Greenberg ([email protected]) on Twitter: "Cybersecurity industry, we need to talk. Is it truly a good idea to call Iranian hackers targeting US seaports, energy and transit systems “Mint Sandstorm”? Or “Charming Kitten”? I wrote (ranted) about the increasingly absurd sprawl of hacker group names. https://t.co/d5nFai8QoQ" / Twitter
https://twitter.com/a_greenberg/status/1650168109431414788
Malware-Analysis/Indirect Syscalls.md at main · dodo-sec/Malware-Analysis · GitHub
https://github.com/dodo-sec/Malware-Analysis/blob/main/Cobalt%20Strike/Indirect%20Syscalls.md
APC warns of critical unauthenticated RCE flaws in UPS software
https://www.bleepingcomputer.com/news/security/apc-warns-of-critical-unauthenticated-rce-flaws-in-ups-software/